Managing Vendor Cybersecurity Risks: Protect Your Business Today
- Feb 23
- 4 min read
In today’s digital world, your business depends on a network of vendors. These vendors provide essential services, software, and support. But here’s the catch: every vendor you work with is a potential entry point for cyber threats. Ignoring this risk is like leaving your front door wide open. You wouldn’t do that, right? So, how do you manage vendor cybersecurity risks effectively? Let’s dive in and explore practical steps you can take right now.
Why Managing Vendor Cybersecurity Risks Matters
You might think, “My vendors are trustworthy. Why worry?” Well, trust is good, but verification is better. Cybercriminals often target vendors because they can be the weakest link. A single breach in a vendor’s system can expose your sensitive data, client information, or financial records. For professionals handling confidential data—like CPAs, tax experts, attorneys, and insurance agents—this risk is even more critical.
Here’s the reality: vendor-related breaches are on the rise. According to recent studies, over 60% of data breaches involve third-party vendors. That’s a staggering number! If you don’t have a solid plan to manage these risks, you’re leaving your business vulnerable.
So, what can you do? Start by understanding the risks and building a strong vendor cybersecurity risk management program. This isn’t just about compliance; it’s about protecting your reputation and your clients’ trust.

Practical Steps for Managing Vendor Cybersecurity Risks
Managing vendor cybersecurity risks might sound complicated, but it doesn’t have to be. Here’s a straightforward approach you can implement today:
1. Identify Your Vendors and Their Risk Levels
Begin by listing all your vendors. Don’t forget those who have access to your systems or data, even indirectly. Next, categorize them based on the level of access and the sensitivity of the data they handle. For example:
High risk: Vendors with access to sensitive client data or financial systems.
Medium risk: Vendors with access to internal systems but no sensitive data.
Low risk: Vendors with no access to your systems or data.
This classification helps you focus your efforts where they matter most.
2. Conduct Thorough Vendor Assessments
Before onboarding a new vendor, perform a detailed security assessment. Ask for their cybersecurity policies, certifications (like SOC 2 or ISO 27001), and recent audit reports. Don’t hesitate to request proof of their security controls.
For existing vendors, schedule regular reassessments. Cybersecurity is not static; vendors’ risk profiles can change over time.
3. Include Security Requirements in Contracts
Make cybersecurity a contractual obligation. Specify the security standards vendors must meet and the consequences of non-compliance. Include clauses about incident reporting timelines and cooperation during investigations.
4. Monitor Vendor Activity Continuously
Set up systems to monitor vendor access and activities. Use tools that alert you to unusual behavior or unauthorized access attempts. Continuous monitoring helps you catch issues before they escalate.
5. Develop an Incident Response Plan Involving Vendors
Prepare for the worst-case scenario. Your incident response plan should include clear steps for working with vendors during a breach. Define communication channels, responsibilities, and timelines.
6. Educate Your Team
Your staff should understand the risks vendors pose and how to spot red flags. Regular training sessions can empower your team to act swiftly and confidently.
By following these steps, you create a robust defense against vendor-related cyber threats.

What is Cyber Security Risk Management?
Cyber security risk management is the process of identifying, assessing, and mitigating risks related to cyber threats. It’s about understanding where your vulnerabilities lie and taking proactive steps to reduce them.
When it comes to vendors, this means evaluating their security posture and ensuring they don’t become a backdoor for attackers. It’s a continuous cycle of assessment, monitoring, and improvement.
Think of it as a shield protecting your business from external threats. Without it, you’re exposed to data breaches, financial losses, and damage to your professional reputation.
Effective cyber security risk management involves:
Risk identification: Knowing who your vendors are and what risks they bring.
Risk assessment: Evaluating the likelihood and impact of potential threats.
Risk mitigation: Implementing controls to reduce risks.
Risk monitoring: Keeping an eye on risks as they evolve.
This approach helps you stay one step ahead of cybercriminals.
Why You Can’t Afford to Ignore Vendor Risks
Let’s be honest: ignoring vendor risks is like playing with fire. The consequences can be devastating:
Data breaches: Sensitive client information exposed.
Regulatory fines: Non-compliance with data protection laws.
Reputation damage: Loss of client trust and business opportunities.
Operational disruption: Downtime caused by cyber incidents.
For professionals handling financial and legal data, these risks are magnified. Your clients expect you to safeguard their information. Failing to do so can cost you dearly.
By investing in vendor cybersecurity risk management, you’re not just protecting data—you’re protecting your business’s future.
How CardinalsByte Can Help You Manage Vendor Cybersecurity Risks
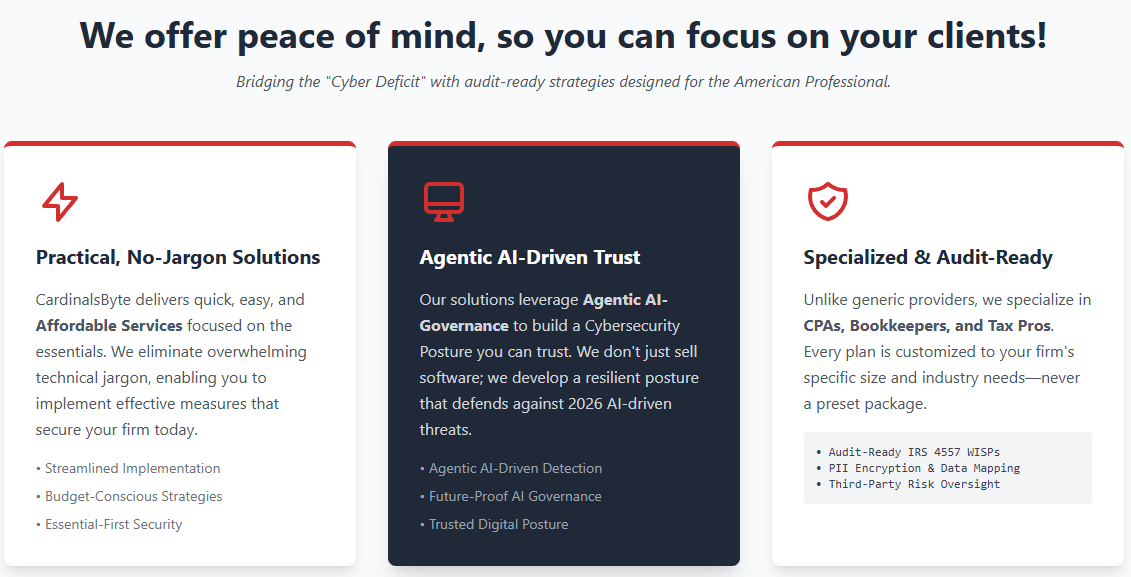
Managing vendor cybersecurity risks is complex, but you don’t have to do it alone. That’s where CardinalsByte comes in. We specialize in helping financial and legal professionals like you navigate these challenges.
Our team offers:
Comprehensive vendor risk assessments
Tailored cybersecurity policies and contracts
Continuous monitoring solutions
Incident response planning and support
Training programs for your staff
We understand the unique pressures you face. Our goal is to take the cybersecurity burden off your shoulders so you can focus on growing your business with confidence.
Don’t wait for a breach to happen. Take control of your vendor risks today with expert guidance.
For more information on how to strengthen your defenses, check out our detailed guide on cybersecurity vendor risk management.
Take Action Now: Secure Your Vendor Relationships
The clock is ticking. Cyber threats are evolving every day, and your vendors could be the weak link. But here’s the good news: you have the power to protect your business.
Start by:
Mapping your vendor ecosystem.
Assessing and categorizing risks.
Enforcing strong security requirements.
Monitoring vendor activities continuously.
Preparing for incidents with a solid response plan.
Remember, managing vendor cybersecurity risks is not a one-time task. It’s an ongoing commitment to vigilance and improvement.
Let CardinalsByte be your partner in this journey. Together, we can build a fortress around your business, keeping cyber threats at bay and your clients’ trust intact.
Don’t wait. Act now. Your business’s security depends on it!




Comments